Ensuring robust cyber defense for endpoint energy assets
Companies across the hydrocarbon supply chain recognize the growing threat of sophisticated, malicious cyberattacks. Many companies continue to struggle to defend early-generation and remote operating assets, such as older compressor stations, which were engineered well before the widespread adoption of digital industrial control systems. As a result, these assets are vulnerable to long-term exposure to emerging cyber-risks, without the ability to be patched easily or updated quickly with the latest security defenses.
Siemens Energy and SparkCognition have collaborated to develop a new cybersecurity system, known as DeepArmor Industrial. The system protects endpoint oil and gas technology assets, including human-machine interfaces (HMIs), by leveraging artificial intelligence (AI) advances to monitor and detect cyber threats, and then deploy patches to ensure operational technology (OT) assets continue running safely and reliably in the field, Fig. 1.

The authors analyze and discuss a variety of real threats associated with increasingly sophisticated, malicious cyberattacks on brownfield and greenfield assets. They also discuss how the DeepArmor Industrial system can be implemented to protect endpoint assets.
Increasingly common cyber threats prove costly and complicated. Consider the following scenario. A pipeline company’s chief information security officer gets a phone call in the middle of the night. One of the company’s compressor stations went down in a remote area in the middle of the night, effectively stopping natural gas transport in a thousand-mile-long pipeline. The problem's root cause is not immediately evident, but it forces producers who use this pipeline to get their product to market through other routes. In addition, customers who rely on just-in-time delivery will have to scramble to find other supply sources. And until the problem can be pinpointed and isolated, the pipeline company cannot guarantee that other compressor stations will not suffer the same fate. This scenario played out in early 2020, when a ransomware attack put a natural gas compression facility out of commission for two days.
Oil and gas companies across the supply chain are recognizing cyberattacks as a real and growing threat to their enterprises. A 2017 study conducted by the Ponemon Institute surveyed global oil and gas companies about their preparedness to respond to cyberattacks. The survey results showed that 67% of respondents believed the risk of cyber threats to industrial control systems had increased over the past few years. This same study found that 61% of respondents said their organization’s industrial control systems protection and security were not adequate. These statistics point to the growing threat that cyberattacks have on the energy industry, which increasingly hinder companies’ physical safety and security, business operations, and other critical infrastructure. Many energy companies with remote, endpoint assets have struggled to defend their environment, because they lack the ability to quickly detect, or the agility to mitigate, cyberattacks that threaten operational technologies.
Cyber threats to brownfield and digitally native assets. The widespread adoption of digital technologies has helped energy companies improve the safety, reliability and efficiency of their operations. Increased connectivity of OT is widely regarded as the key to these improvements. At the same time, this connectivity has expanded these operations’ exposure to cyberattacks.
While cyberattacks can successfully strike both older, brownfield assets and newer equipment installed with digital technologies from the outset, these systems are vulnerable for varied reasons. Older compressor stations still rely on a combination of analog equipment and digital retrofits. Many of these facilities are in remote locations along a pipeline, meaning that they operate for extended periods without direct human interaction or involvement. This equipment may only connect to networks when annual updates are required or receive updates from technicians when they visit the site. This isolation results in longer exposure to emerging risks and increased maintenance expenses.
For newer equipment, such as a smart meter or digitally native compressor station, the OT is connected continuously to information technology (IT) networks. Through this connectivity, which is a critical component of the industrial internet of things (IoT), technicians can monitor metrics, diagnose problems, and make software upgrades without having to visit the site. However, the same connectivity that enables such rapid updates and efficient operations management also increases exposure to cyberattacks. Attackers can easily use the same network and tools to introduce malware, Fig. 2.
The critical need for patching. Regardless of the equipment's age and digital sophistication, operators cannot afford to let their security measures fall behind, as new attack methods and cyber threats increasingly target energy infrastructure. Software patches must be installed regularly to deal with new threats on remote assets—a process that has proven technologically and economically challenging for many companies.
As a result, some companies have developed a “can’t patch, won’t patch” mentality regarding some of their assets. Systems under the “can’t patch” category are typically older machines that cannot be patched because the original equipment manufacturer (OEM) no longer provides patches, such as Windows XP or Windows 7. The “won’t patch” mentality is linked to the perceived criticality of a system or piece of equipment. A system that is not considered a critical part of the operation may not get routine patching updates because the potential threat is considered low enough that the time and expense of patching are not justified.
Adhering to either of these ideas risks the asset’s safety, operability, profitability and potential outages for the companies. However, even the most robust patching program may include intervals where patches are not easily or quickly deployed to isolated or intermittently connected sites. This leaves systems vulnerable to new threats before they are widely known.
Novel endpoint monitoring and protection. These challenges have driven the need for monitoring tools that increase the chance of detecting an attack while it is happening. Access to real-time data lets operators identify and investigate anomalies. In addition, automated monitoring solutions provide constant tracking and vigilance to quickly recognize site conditions or user behaviors that suggest a threat and enable early interventions to minimize the threat’s spread to other systems.
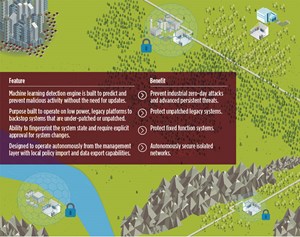
Meeting these needs was the goal behind the development of DeepArmor Industrial, powered by Siemens Energy, which perpetually looks for cyber threats for vulnerable endpoint OT assets—whether they are isolated in the field or continuously connected. This constant monitoring solution also deploys patches to keep critical equipment safe until security experts can update protocols in the field.
Unlike existing endpoint solutions, this cybersecurity solution incorporates artificial intelligence to provide a defense layer independent of threat intelligence, thus eliminating the need for threat signature updates or specialized analysts to secure OT systems individually. The solution uses behavioral analysis to continuously monitor and detect new threats, resulting in both a first line of defense and immediate protection against previously identified and zero-day attacks on endpoint devices.
Such features provide robust cybersecurity measures to prevent or mitigate attacks, even novel threats still unknown to the industry, while reducing asset owners' security costs. The system can be installed early in the week, receive no updates all week, and remain an effective defense at the end of the week—even for new threats that emerge in the days in between.
The solution’s intelligent defense and detection capabilities, customized design, and site-specific deployment model deliver secure solutions. The AI-based defense system uses a predictive approach to prevent ransomware, viruses, and other advanced malware from executing. Data science models, which leverage unique threat detection IP and methodology, are hosted individually, and executed on-device to help deliver high efficacy against zero-day attacks.
The monitoring system significantly reduces false positives and the costs to update physically distant assets. It vastly improves cyber resiliency from the first day of installation through pre-trained AI algorithms that detect and protect against known and unknown threats. It also helps prevent industrial attacks in disconnected OT environments, including industrial HMIs, engineering workstations, engineering notebooks, data stores, and historians.
Because AI capabilities are built into this monitoring solution, it does not require patches and can support old versions of Windows natively. This gives users the IT technology of a next-generation, endpoint protection product, installed into an OT-architected product that runs on everything from Windows 2000 to current Windows releases such as Windows 10 and Server 2019.
Deploying the system for a tailored defense approach. Because few sites in the energy sector are homogenous, installation of this cyber threat monitoring solution is not a “one-size-fits-all” proposition. The process begins with Siemens Energy’s service team members gaining a deep understanding of the unique organizational and technical needs within the asset’s operational environment. This includes a careful review of the network architecture to identify the most effective placement of AI-driven, OT endpoint protection. The service team helps owners evaluate their assets and prioritize defense strategies based on three risk criteria:
- Connectivity, which affects the magnitude of exposure to attack.
- Operational importance, which indicates the severity of impacts on the business, if attacks disrupt the normal function of the equipment or system.
- The maintenance schedule, which indicates the length of intervals in between defense updates, as well as the difficulty or expense of updates.
A customized deployment approach is designed with these criteria in mind, to ensure that the installed solution meets the asset owner’s endpoint protection needs. For example, consider two identical servers purchased from the same manufacturer. The first is installed at a remote site, where it logs the activities of a pumping station. The second is installed at a company’s flagship facility, supporting an HMI critical to managing several parts of the plant. In this example, tight restrictions, as regards which applications one can execute on the server, would help secure the remote site. However, these same restrictions might disrupt or curb critical workflows at the flagship site.
The service provider’s understanding of the energy supply chain, coupled with the monitoring system’s protection, gives asset owners a clear picture of their risk profile—both in terms of the identified vulnerabilities at their sites and the operational impact that an attack could have by exploiting these vulnerabilities. This analysis enables asset owners to prioritize high-risk, high-value targets and select defense architecture and technology appropriate to the site.
Assured cybersecurity for long-term asset optimization. In today’s rapidly changing and unpredictable energy sector, the need for robust cybersecurity protections is critical to asset owners’ reliable operability and profitability. This new monitoring system is proving itself to be a differentiating solution for today’s cybersecurity environment, as attacks on the energy sector increase in frequency and sophistication, Fig. 3. The AI-based solution offers an unprecedented level of protection to endpoint assets of varying application and age. The always vigilant, customizable cybersecurity solution protects critical assets from cyberattacks—whether intermittently connected in a remote operating environment or continuously connected to the network.
The cognitive endpoint protection afforded by this monitoring solution gives the asset owner accurate, early-warning failure prediction. By identifying and isolating cyber threats quickly, this monitoring solution prevents costly asset failures, reducing unscheduled downtime while optimizing asset performance. This solution also provides detailed, actionable insights that asset owners can use to safeguard their assets from newer cyber threats.
Consider the compressor station scenario presented earlier, but now with the addition of DeepArmor Industrial at the asset. This time, the chief information officer gets an email in the middle of the night from the company’s security operations center. The monitoring system detected an anomaly at one of the compressor stations. The system immediately interrupted the execution of the malicious code, prevented the system from being wiped, and flagged the incident for analysis.
A technician realized that malware had been inadvertently loaded onto the system during the previous update. The system was immediately reverted to an older software patch, and the technician quickly identified the malware that had infected the device. The technician notified his colleagues of the newly identified malware and shared the threat intelligence with the industry. Future patches will be designed to defend against this new threat.
As such incidents become more common, the innovative, AI-driven DeepArmor Industrial system is delivering next-generation antivirus, threat detection, application control, and zero-day attack prevention to endpoint assets across the energy production, generation, transmission, and distribution chain. For the first time, asset owners have access to a system that brings fleet-level cybersecurity monitoring and protection capabilities—for today’s cyberattacks and emerging, future threats.

- Executive viewpoint: Methane monitoring goes digital (May)
- Why oil and gas companies should invest in ruggedized edge computing (May)
- What's new in production: When everything is going wrong at the same time (April)
- Regional Report: Brazil reaches for new heights in 2026 (March)
- What's new in exploration: I bet you wish you had kept your Exploration priority today! (March)
- What's new in production: Things go better with Coke (February)
- Subsea technology- Corrosion monitoring: From failure to success (February 2024)
- Applying ultra-deep LWD resistivity technology successfully in a SAGD operation (May 2019)
- Adoption of wireless intelligent completions advances (May 2019)
- Majors double down as takeaway crunch eases (April 2019)
- What’s new in well logging and formation evaluation (April 2019)
- Qualification of a 20,000-psi subsea BOP: A collaborative approach (February 2019)


